Important things to know
It's 11 PM on a Tuesday. You're sitting at your desk with fourteen browser tabs open. One tab has a Reddit thread about breaking into cybersecurity. Another has a YouTube video titled "SOC Analyst Day in the Life" paused at the three-minute mark. You've bookmarked three different certification study guides, downloaded two free ebooks, and signed up for a platform you haven't logged into yet. You feel like you've been "researching" for weeks, maybe months, but you haven't actually started anything.
If that sounds familiar, I've been where you are.
Three years ago, I was working as a video editor and digital marketer, Googling "how to get into cybersecurity" at least twice a week. Every article I found told me something different. Get the CompTIA Security+. No, learn Python first. No, build a home lab. No, get a degree. The advice was endless, contradictory, and honestly paralyzing.
Here's what I wish someone had told me back then: you don't need to learn everything. You need to learn the right things, in the right order, and you need to start doing before you feel ready. That's what this post is. Not a list of resources you'll bookmark and forget. A roadmap. Six months, broken down into what to focus on each month, what tools to touch, and what "learning" actually looks like when you're trying to land your first SOC analyst role. Let's get into it.
What a SOC Analyst Actually Does (The Real Version)
Before we talk about how to become one, let's clear up what the job actually involves. Because the textbook version and the real version are pretty different.
The textbook will tell you a SOC analyst "monitors an organization's network for security threats and responds to incidents." That's technically accurate. It's also about as useful as saying a chef "prepares food."
Here's what a typical day actually looks like for a Tier 1 SOC analyst.
You log in and check the queue. There are alerts. Lots of them. Most are false positives. Your job is to figure out which ones are real and which ones are noise. You're looking at logs from firewalls, endpoints, email gateways, and sometimes cloud platforms. You're using a SIEM (Security Information and Event Management tool) to correlate data, and you're checking indicators of compromise against threat intelligence feeds.
When something looks suspicious, you dig deeper. Maybe a user's account logged in from two countries within an hour. Maybe a workstation is reaching out to a domain that was registered yesterday. You investigate, document what you find, and either close the alert or escalate it to someone more senior.
You'll write a lot of notes. You'll follow runbooks (step-by-step procedures for handling specific alert types). You'll sometimes feel like a detective, and you'll sometimes feel like you're doing data entry. Both feelings are accurate.
The unglamorous truth? A huge part of the job is pattern recognition and documentation. It's not hacking. It's not red team movie scenes. It's methodical, detail-oriented work. And honestly, that's what makes it a great entry point, because the core skills are learnable, even if you're starting from scratch.
The 6-Month Roadmap
A quick note before we dive in: this roadmap assumes you can dedicate roughly 2 to 3 hours a day to learning. If you have more time, you can move faster. If you have less, it might take a bit longer. That's fine. Consistency beats intensity every time.
Month 1: Build the Foundation (Networking and Operating Systems)
You cannot do security work if you don't understand what you're securing. This is where most people make their first mistake. They jump straight into "hacking" tutorials or certification prep without understanding how networks and systems actually work. Then they hit a wall three weeks later because they don't know what a subnet is or why DNS matters.
Month one is about building that base.
Networking fundamentals. You need to understand how data moves. Learn the OSI model, but more importantly, learn TCP/IP. Understand what happens when you type a URL into a browser. Learn about DNS, DHCP, HTTP/HTTPS, ARP, and common ports and protocols. You don't need to memorize every RFC, but you need to be comfortable reading a packet capture and understanding what's happening.
Operating systems. Get comfortable with both Windows and Linux. For Windows, learn how to navigate Event Viewer, understand basic Active Directory concepts (users, groups, policies), and know where logs live. For Linux, get familiar with the command line. Learn to navigate the file system, use grep, cat, less, find, and manage permissions. You'll use Linux constantly in security tooling.
What to actually do this month:
Install VirtualBox or VMware on your machine. Set up a Windows VM and an Ubuntu VM. Practice using them. Open a terminal and break things on purpose, then figure out how to fix them. Follow along with Professor Messer's free CompTIA Network+ videos on YouTube. You don't need to take the exam right now, but the content is exactly what you need. Download Wireshark and capture your own network traffic. Just look at it. Click around. Get familiar with what normal traffic looks like.
Reality check: This month will feel boring if you came in expecting to analyze malware on day one. That's okay. Every experienced analyst I know will tell you the same thing: networking knowledge is what separates analysts who can actually investigate from those who just click buttons in a SIEM without understanding what they're looking at.
Month 2: Security Fundamentals and the CompTIA Security+
Now that you have a foundation, it's time to layer security concepts on top of it.
The CompTIA Security+ is the single most recommended certification for breaking into cybersecurity, and for good reason. It's vendor-neutral, widely recognized, and covers the breadth of topics you'll encounter in a SOC. More importantly, a lot of job postings for entry-level SOC roles either require it or list it as preferred.
What to focus on: Threats, attacks, and vulnerabilities. Security architecture and design. Identity and access management. Risk management. Cryptography basics. Incident response concepts.
You don't need to become an expert in all of these. You need working knowledge. When someone mentions a brute force attack, a phishing campaign, or a man-in-the-middle scenario, you should know what they're talking about and roughly how it works.
What to actually do this month:
Start studying for the Security+ using a structured resource. Professor Messer's free video series is solid. If you want a book, Jason Dion's study guide or the official CompTIA study guide both work well. Do practice questions daily. Not just reading, actually testing yourself. Active recall is how you learn, not passive watching. Start a simple study journal. Write down one thing you learned each day in your own words. This habit pays off later when you're prepping for interviews.
Reality check: The Security+ is a multiple-choice certification exam. Passing it proves you understand concepts, but it doesn't prove you can do the job. Don't make the mistake of thinking the cert alone will get you hired. It opens doors, but your hands-on skills are what close the deal in interviews.
Month 3: SIEM Basics and Log Analysis
This is where things start getting real. Month three is when you transition from "learning about security" to "doing security stuff."
A SIEM is the primary tool you'll use as a SOC analyst. It collects logs from across an organization (firewalls, servers, endpoints, cloud services), correlates them, and generates alerts when something looks off. Learning to navigate a SIEM and read logs is arguably the most important practical skill for a Tier 1 analyst.
What to actually do this month:
Sign up for a free Splunk account and go through the Splunk Fundamentals 1 course. It's free, and Splunk is one of the most widely used SIEMs in the industry. Even if your future employer uses something different (Microsoft Sentinel, IBM QRadar, Elastic SIEM), the concepts transfer. Learn SPL (Splunk Processing Language) basics. How to search, filter, and build simple queries. This is the security equivalent of learning SQL for a data analyst.
Practice reading raw logs. Windows Event Logs are a great place to start. Learn to recognize common Event IDs: 4624 (successful logon), 4625 (failed logon), 4688 (process creation), 4720 (user account created). These come up constantly in real investigations. Download sample log files (BOTS datasets from Splunk are excellent) and practice investigating them. Try to answer questions like: "What IP address was responsible for the most failed login attempts?" or "Which user account was created at an unusual hour?"
Reality check: Log analysis is not glamorous, but it's the bread and butter of SOC work. I've seen people spend months studying for certifications and then freeze when they see actual log data because they never practiced reading it. Don't be that person. Get comfortable with messy, real-world data now.
Month 4: Incident Response and Threat Intelligence
By now you have networking knowledge, security concepts, and SIEM skills. Month four is about learning what to do when something bad actually happens.
Incident response is the structured process of identifying, containing, eradicating, and recovering from a security incident. As a Tier 1 analyst, you won't be leading incident response, but you will be the first person to triage an alert and decide if it's worth escalating. That decision matters.
What to focus on: The NIST Incident Response Lifecycle (Preparation, Detection & Analysis, Containment/Eradication/Recovery, Post-Incident Activity). How to triage alerts. The difference between a true positive, false positive, benign true positive, and false negative. How to write clear, concise incident notes that your teammates can understand at 3 AM.
What to actually do this month:
Read the NIST SP 800-61 (Computer Security Incident Handling Guide). It's dry, but it's the framework most SOCs are built around. You don't need to memorize it, but you should be familiar with the phases.
Start practicing with free platforms. LetsDefend.io has an excellent SOC analyst simulation where you get realistic alerts and walk through investigation steps. It's one of the closest things to real SOC work you can get without actually having the job. Blue Team Labs Online is another great option for hands-on defensive security challenges.
Learn the basics of threat intelligence. Understand what IOCs (Indicators of Compromise) are: IP addresses, domains, file hashes, URLs associated with known threats. Practice checking IOCs against free tools like VirusTotal, AbuseIPDB, and URLhaus. This is something you will do every single day in a SOC.
Reality check: Most beginners underestimate how important communication and documentation are in incident response. You can be technically brilliant, but if you can't clearly explain what you found and what you did about it, you'll struggle in the role. Practice writing investigation summaries. Even if you're just investigating practice alerts, write up your findings as if your manager is going to read them.
Month 5: Hands-On Projects and Building Your Portfolio
You've been learning for four months. Now it's time to prove it.
Here's something that might surprise you: hiring managers for SOC roles care less about your degree or certifications than you think. What they really want to see is evidence that you can think like an analyst. That you can investigate, reason through a problem, and communicate what you found.
A portfolio of hands-on projects does that better than any certification ever will.
What to actually do this month:
Build a home lab. This doesn't have to be expensive or complicated. Use VirtualBox to set up a small network: a Windows machine, a Linux machine, and maybe a pfSense firewall. Install the Elastic Stack (Elasticsearch, Logstash, Kibana) as a free SIEM alternative. Generate traffic, create alerts, and practice investigating them. Document the whole process.
Complete at least 5 to 10 challenges on platforms like CyberDefenders, Blue Team Labs Online, or TryHackMe's SOC Level 1 path.
Write up your process for each one. Not just the answer, but how you got there. What tools did you use? What did you look at first? What was a dead end? What confirmed your theory?
Start a blog or a GitHub repository where you document your work. It doesn't have to be fancy. A simple GitHub repo with markdown write-ups of your investigations is enough. This gives interviewers something concrete to ask you about, and it shows initiative that 90% of other candidates don't demonstrate.
Contribute to the community. Answer questions on Reddit's /cybersecurity or /SecurityCareerAdvice. Join Discord servers like John Hammond's community or the Black Hills Information Security group. Networking with other people on the same journey keeps you motivated and occasionally leads to opportunities.
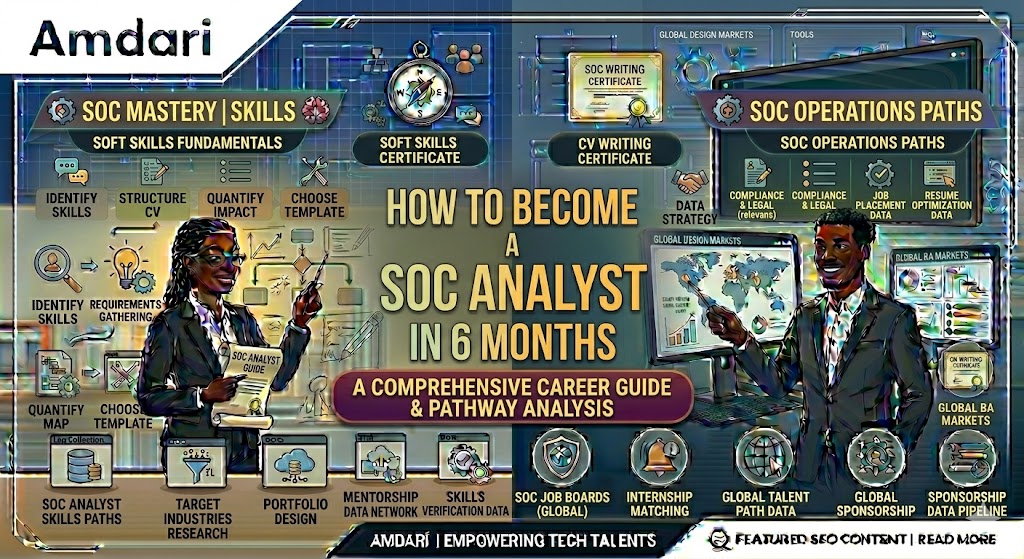
Reality check: Your home lab doesn't need to be perfect. Your write-ups don't need to be polished. They need to exist. I've interviewed candidates who claimed they had "extensive lab experience" but couldn't describe a single investigation they'd done. Show your work. If you find yourself struggling to structure these investigations or wanting guided scenarios that walk you through real SOC workflows, platforms like Amdari offer hands-on project environments designed specifically for this ,building the kind of documented, portfolio-ready work that hiring managers look for.
Month 6: Certifications, Resume, and Interview Prep
The final stretch. If you haven't taken the Security+ yet, this is the month to do it. If you already passed it, consider whether an additional certification makes sense. The CompTIA CySA+ (Cybersecurity Analyst) or the Splunk Core Certified User are both solid choices that directly align with SOC work.
But certifications are only one piece of the puzzle this month. The bigger focus is making yourself hireable.
Your resume. Keep it to one page. Lead with a skills section that lists specific tools and technologies: Splunk, Wireshark, Windows Event Logs, Linux CLI, SIEM operations, log analysis, incident triage. If you have IT experience (help desk, system admin, networking), frame it in security terms. "Monitored and resolved user access issues" becomes "Managed identity and access controls for 200+ user accounts, investigating anomalous login activity." If you don't have IT experience, your projects section becomes even more important. List your home lab, your write-ups, your completed challenges.
Interview preparation. SOC analyst interviews typically have three components: behavioral questions, technical questions, and scenario-based questions.
For behavioral questions, prepare stories about problem-solving, teamwork, and handling pressure. The STAR method (Situation, Task, Action, Result) works well here. Even if your examples come from non-security jobs, the skills transfer.
For technical questions, expect things like: "Walk me through what happens when you type a URL into a browser." "What's the difference between TCP and UDP?" "What Windows Event ID indicates a successful logon?" "How would you investigate a phishing alert?" "What is a false positive and how do you handle it?" You should be able to answer all of these confidently by now.
For scenario-based questions, you'll often get something like: "You see an alert for a user downloading a large amount of data at 2 AM. Walk me through your investigation." This is where your months of practice pay off. Talk through your process step by step. What logs would you check? What tools would you use? What would make you escalate versus close the alert? Oh, how I love Amdari, they are experts in this field which involves interview prep sessions as well as CV optimization so, you might want to check them out at this point.
What to actually do this month:
Take the Security+ if you haven't. Apply to at least 10 positions per week. Tailor your resume for each application (it takes five minutes and makes a real difference). Practice interview questions out loud, not just in your head. Record yourself answering and listen back. It's uncomfortable, but it works.
Don't only apply to jobs titled "SOC Analyst." Also look for "Security Operations Center Technician," "Security Monitor," "Cyber Defense Analyst," "Information Security Analyst I," and "IT Security Specialist." The same role goes by many names. Also consider managed security service providers (MSSPs). They hire in volume, often provide training, and the exposure you get working across multiple client environments is incredibly valuable early in your career.
Reality check: You will probably not get the first job you apply for. Or the fifth. Or maybe even the fifteenth. That's normal. The cybersecurity job market for entry-level roles is competitive. But most of your competition is people who got a certification and nothing else. If you've followed this roadmap, you have a foundation, hands-on skills, a portfolio, and the ability to talk intelligently about real investigations. That puts you ahead of the vast majority of applicants.
Building Experience When You Don't Have a Job Yet
This is the part nobody talks about enough. How do you get experience when every job posting wants experience? The answer is that you create it with opportunities like the SOC Analysis work experience internship which career switchers and African immigrants in the UK, US & Canada utilise to work on projects, build their confidence and increase their chances of landing jobs. Click here to book a free career clarity call with a consultant in our team to find out how we can help you get started.
Volunteer; non-profits and small businesses often have zero security oversight. Offer to review their security posture, help set up basic monitoring, or write a simple incident response plan. You'll learn a lot, and you'll have a real project to talk about.
Participate in CTF competitions. Capture The Flag events, especially blue team and DFIR (Digital Forensics and Incident Response) focused ones, give you structured problems to solve under time pressure. They're fun, they're educational, and they look great on a resume.
Follow real-world incidents. When a major breach hits the news, read the technical reports. Companies like Mandiant, CrowdStrike, and Microsoft publish detailed write-ups of significant incidents. Read them and try to understand the attack chain. What was the initial access vector? How did the attacker move laterally? What indicators were left behind? This kind of analysis builds the investigative thinking muscle you'll need on the job.
Use free training platforms relentlessly. TryHackMe, LetsDefend, CyberDefenders, Splunk's free training, and SANS Cyber Aces are all available to you right now. There has never been more free, high-quality security training available. The only barrier is whether you actually use it.
Six months is enough time to become a competitive candidate for a SOC analyst role. It's not enough time to become an expert. And that's perfectly fine. Nobody walks into their first SOC job knowing everything. The learning curve is steep, and you'll spend your first few months on the job feeling like you're drinking from a fire hose. Every analyst I know felt that way. The ones who succeeded were the ones who asked questions, took notes, and stayed curious.
The path into cybersecurity is not a straight line. You'll have weeks where you feel like you're making real progress and weeks where you feel completely lost. You'll apply for jobs and hear nothing back. You'll bomb at least one interview. These are not signs that you're failing. They're signs that you're actually in the process.
The people who make it into this field aren't the ones who waited until they felt ready. They're the ones who started before they were ready and figured it out along the way.
So close a few of those browser tabs. Pick one thing from Month 1. And start today.
Not tomorrow. Today.